Safeguarding
Our Kids and Your Staff.
People + Culture
Child Safeguarding
Workplace Health & Safety
Mental Health / Psychosocial Hazards
And so much more!
Certified By empowers community non-profits and smaller businesses with a simplified, automated, and affordable way to proactively manage their safeguarding responsibilities.
As the first and only platform specifically designed for the nuanced needs of smaller organisations, we make governance, risk, and compliance (GRC) accessible, enabling you to protect what matters most without the complexity or cost traditionally associated with compliance solutions.
Child Safeguarding
Clubs looking to understand, measure and improve child safeguarding standards.
Health & Safety
Smaller businesses committed to protecting their most valuable assets.
Human Resources
Empowering smaller businesses to stand out as an employer of choice.
Compliance shouldn’t be a burden.
It’s an opportunity to differentiate yourself.
As the modern world becomes more complex and regulated, the cost and effort required to manage safeguarding responsibilities can be overwhelming. However, not doing so can be even more costly in terms of lost revenue, legal fees, and damage to your reputation.
This is where Certified By comes in.
As a game changing AI enabled SaaS #RegTech platform offering affordable and infinitely scalable online risk-based programs modelled on best practice standards, we make it easy for businesses and community organisations to assess, report, remediate, improve, review and certify. Our platform helps you mitigate risks, improve compliance posture, and build trust in brand to power growth.
How it Works
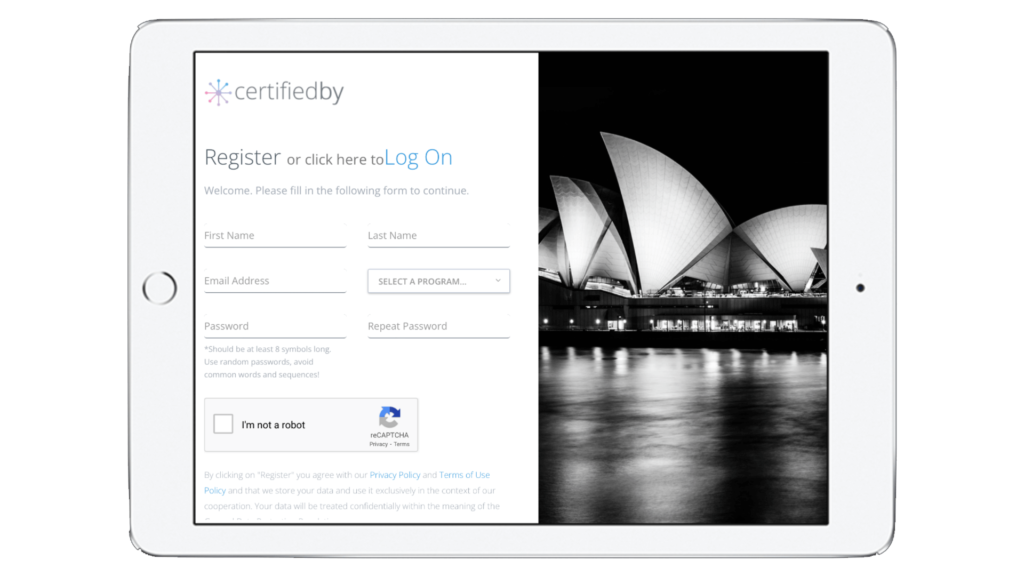
REGISTER
Simply click the START NOW button at the top of this page to start your program.
IMPROVE
For smart recommendations, supporting information and helpful resources, subscribe to the Action Management Module (see more).
CERTIFY
Evidence results with a Program Review and Certificate of Assessment to share with relevant stakeholders (see more).
Choose Your Own Adventure…
Child Safeguarding
Club & community non-profits needs to protect, detect, respond to and recover from threats to child safety, but most don’t know where to start.
Health & Safety
Maintaining best practice standards is essential for any business, but it can be difficult to know where to start or how to keep up with changes in legislation.
Vic Child Safety Standards
The Victorian Child Safe Standards are the new framework for safeguarding children and young people, and compliance is compulsory.
ALL PROGRAMS include access to a digital library of amazing tools & resources!
The GRC Survival Guide
Tailored for go-getters, this guide cuts through the noise to deliver actionable strategies in Governance, Risk, and Compliance. More than just advice – it’s a blueprint for success. Avoid pitfalls, make smart decisions, and drive your business towards sustainable growth. Don’t miss out on this opportunity to turn information into power.
The GRC Survival Guide

Good Vibes



Start your GRC journey
Disclaimer 🤚
We’ve put our heart and soul into building something to help millions of SMEs & nonprofits around the world.
We’ve done a lot right and made mistakes along the way, cause no one ever said #RegTech and risk management services were easy. Rest assured we are leveraging the brightest minds, deepest resources, connected partnerships and hunger for growth to develop a better product every day for you.
With that being said… In no event shall CertifiedBy, its affiliates, partners, or licensors be liable for any direct, indirect, incidental, special, consequential, or punitive damages, including but not limited to, lost profits, lost data, business interruption, or other losses arising out of or in connection with the use of, or inability to use, the CertifiedBy platform or any content, advice, or recommendations generated by the platform.